MGTC50
Commerce Ventures
A 3rd year undergraduate course in the
Division of Management, University of Toronto, Scarborough College, Canada
 |
MGTC50Commerce Ventures A 3rd year undergraduate course in the Division of Management, University of Toronto, Scarborough College, Canada |
| Section A | Section B | Section C | Section D | Section E |
| Security
- whether it be credit card misuse or email messages being infected with
a virus, - continues to be one of the most significant impediments to the
successful spread of e-commerce. Therefore, in order to have a good grasp
on "building Internet Commerce ventures", it is necessary to include a
good discussion of security topics.
WTGR |
 |
Before we begin
this section, it is perhaps wise to pause and reflect on whether the precautions
we are about to discuss are necessary - that is to say "why deal with the
trouble of security procedures if the threat, in actuality, is not very
big?"
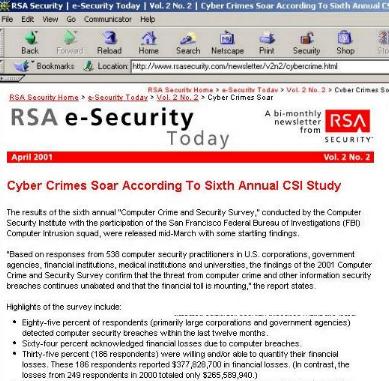
The answer to this question is a resounding YES - the threat is real and it is growing. We searched for an authoritative voice on threat trends and found the article below - this article discusses a survey conducted by the Computer Security Institute (a legitimate and credible organization) and the FBI's Computer Intrusion squad based in San Francisco. The survey concludes that cyber crimes are rising substantially - therefore the threat is real and it needs to be dealt with. |
| "The results
of the sixth annual [2001]"Computer Crime and Security Survey," conducted
by the Computer Security Institute with the participation of the San Francisco
Federal Bureau of Investigations (FBI) Computer Intrusion squad,
were released mid-March [2001] with some startling findings. "Based
on responses from 538 computer security practitioners in U.S. corporations,
government agencies, financial institutions, medical institutions
and universities, the findings of the 2001 Computer Crime and Security
Survey confirm that the threat from computer crime and other information
security breaches continues unabated and that the financial toll
is mounting," the report states."
www.rsasecurity.com/newsletter/v2n2/cybercrime.html |
 |
| . | After reading the story
in the RSA page about the Survey concluding Cyber Crime is growing, you
should pause and reflect if
1. Cyber Crime is growing, or is it also partly 2. Companies are simply getting better about detecting cyber crime. |
| Counter
measures Counter
|
Responding to a security
risk, or a threat of a security risk
|
| Security
Considerations Proper
|
|
| Security
Considerations Proper
|
Security Procedures:
Weak Points
|
||||
 |
Secrets &
Lies: Digital Security in a Networked World
- information about this book can be obtained from www.witiger.com/ecommerce/ecommercetextssecurity.htm Schneier talking about the "relationship between prevention, detection and reaction. "Good security encompasses all three"
|

Chpt 5
|
"Electronic Commerce":
Greenstein & Feinman, Chpt 5 The Risks of Insecure Systems
- information about this book can be obtained from www.witiger.com/ecommerce/ecommercetextssecurity.htm the powerpoints for Chpt
5 can be obtained from
"Until recently, most information security breaches were initiated by insiders. However a study by the CSI Computer Security Institute and FBI indicates that this trend is rapidly changing. The findings indicate that the number of external attacks is growing because if the increased use of the Internet" Overview of Risks Associated
with Internet Transactions
risks associated with transactions between business partners risks associated with confidentially-maintained archival, master file and reference data risks associated with viruses and malicious code overflows |
Chpt 3 Types of
Types of
|
Secrets &
Lies: Digital Security in a Networked World
by Bruce Schneier Chpt 3 Attacks
|
Chpt 3 Types of
- Frauds |
|
Chpt 3 Types of
- Scams |
Scams
Schneier quotes the National Consumers League (Chpt 3, page 24) "the five most common online scams are
|
 |
Privacy Violations
In many countries, people do not own the information which is collected about them, that is to say, their personal data. This information is considered the property of whatever credit card company, insurance firm, educational institution that collected the information. As a consequence of some outrageous violations of collecting and disseminating personal information, Canada, New Zealand and other countries have enacted tough laws which are binding on the companies that collect and pass on personal profile information (which we noted in Section 1 of this course when we presented the federal and provincial legislation dealing with this). Privacy violations are not, strictly speaking, criminal activity, but, depending on what is done with the information, it can be used for criminal purposes - such as assuming an identity for the purposes of obtaining credit, which could then be used to fraudulently buy products and services. As a person studying e-commerce, it would be your responsibility to understand that protecting the private personal information of people that have data held within your firm's IT systems, is critical to conduct effectively and without risk. |
Chpt 3 Types of
- Privacy Violations |
Privacy Violations
Schneier, page
29
If the attacker wants to know everything about

Data Harvesting
Data harvesting is only worthwhile
doing if it can be automated, and computers allow the automation process
to be done very effectively. Using good cryptography will thwart harvesters
since they will not be easily able to identify if what they are looking
for is in the target they are attacking.
|
Chpt 3 Types of
Types of
|
Secrets
& Lies: Digital Security in a Networked World
by Bruce Schneier Chpt 3 Attacks
Schneier gives an amusing example noting that in the hours leading up to the 1991 bombing of Iraq, pizza deliveries to the Pentagon increased one hundredfold - even if you did not know what the generals and admirals were talking about, it had to be something important from which there would be some serious time spent on decision making.
|

| Internal
Threats |
Internal
Threats
|
| Internal
Threats |
Internal
Threats, Logic Bombs
|
 |
The disgruntled
employee poses but one of many insider threats to information systems
and the valuable data stored therein. Unauthorised access from insiders,
rather than outside hackers, accounted for 44% of network security breaches
last year, according to the March 2000 survey by Computer Security Institute
(CSI) and the FBI.
"The greatest exposure to any organisation is what I call the knowledgeable insider - anybody from a janitor to a vendor or an active or ex-employee," says Steve Dougherty, director of information security at the Fulsom, California-based California Independent System Operator, which is taking over management of power grid transmissions for 27m Californians with the states recent industry deregulation. American Society for Industrial Securitys (ASIS). 89% of respondents to the ASIS 1997/1998 Intellectual Property Loss Special Report indicated that their biggest concern regarding system security is retaliation from disgruntled employees.. |
| University
College computers - a weak link |
|
| Risks
With Business Partners they
may
Risks
they
may
|
Microsoft - which one would presume is very very careful about who they partner with, is often vulnerable when the partner makes a bad mistake. Some of these mistakes happen when the intermediary is responsible for dispensing some service, such as making downloads available. In the screen capture below, you can see Prof. Richardson has received an email from SANS. This email details how Microsoft Hotfixes downloaded from the Premier Support and Gold Certified Partner web sites were infected with the Fun Love virus. 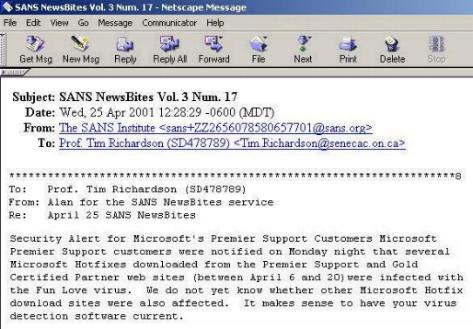 The original email has been
uploaded to the ECP site and you can read the full text, including other
warnings and info at
|
 |
It is not the
intention of this part of the course to be able to adequately cover all
the various types of viruses that may effect e-commerce since do not have
the time nor resources to do that satisfactorly -
but, it is important to have some understanding of the business risk at stake here and try to evaluate if it is a serious problem, because - if it is a serious problem, then every e-commerce professional needs to add to their portfolio of knowledge, some degree of understanding about viruses. |
 |
This web site is very helpful and you are encouraged to bookmark it and check it for terms you do not know. |
|
Virus Protection and business risk Virus
|

"IT's Battleground: The Quest for Virus Protection" is the title of an August 4th, 2000 in Computing Canada www.plesman.com/Archives/cc/2000/Aug/2616/cc261614a.html In this August 4rth article
it is noted that
From the August 4rth article "Symantec, publisher of the market-leading Norton Anti-Virus, has seen an average of 115 new viruses each month this year, up 30 per cent from 1999." |
| Viruses | "Virus Vigilance
"
is the title of a December 11, 2000 article in Computerworld written by Deborah Radcliff http://www.surfcontrol.com/news/articles/content/12_11_2000_cw.html In this Dec 2000 article it is noted that "The problem with today's viruses is twofold: Not only can they be easily rewritten to change their signatures and bypass antivirus tools, but they are also tempting attachment types for click-happy users who see nothing wrong with opening mail attachments from trusted sources. " translated 1. viruses can change form so the anti-virus software you installed, and obediently updated, cannot recognize the new virus as a threat, and does not screen it outSo, what is the problem when people don't listen, andfollow proper procedures to protect against viruses? Radcliff quotes Roland Cuny,
chief technology officer at Webwasher.com, an Internet content filtering
vendor
What is part of a technical solution to block viruses? Radcliff quotes experts saying
you can "...set up filters to block executable attachments before they
get to desktops. Blocking file types known to carry viruses and Trojan
horses (hidden programs) may sound extreme. Bruce Moulton, vice president
of infrastructure risk management at Fidelity Investments in Boston said
he first reviewed how his company uses these file types. Once he determined
that these attachments weren't even used for business purposes, making
the decision to block them was easy. "The business impact of shutting out
these file types is zero because 99.9% of these attachments that come in
are for personal viewing, like animated Christmas cards, movie clips,
things like that,"
|
| Worm
Viruses Worm
Worm
Viruses Worm
Worm
Worm
|
.
What does it do? "Code Red, named for a caffeinated soft drink favored by computer programmers, scans the Internet for other computers to infect, and as more computers are infected the scanning gets more widespread and could slow Internet traffic to a crawl. The worm can
also defaces sites, though in two of the three known variants
no vandalism is apparent to computer users. In last week's hits, some U.S.
government sites showed the message ''Hacked by Chinese!'' but the Chinese
government said the worm probably did not come from China."
"Government agencies in Canada
and the United States, as well as academics and Web security experts, were
monitoring the situation closely, but did not detect any slowdown right
after the worm's expected arrival at 8 p.m. EDT., July 31, 2001"
|
| Before we finish the section on viruses, it would be worthwhile to visit the Security Section on Netscape's site. There is a short Q&A about viruses and a helpful glossary. |  |
| . | While
there are some news reports and insightful web sites we can reference which
seem to indicate where things are going - there is not a lot of hard core
knowledge about the future of the internet - why?
|